Foxcatcher - Chasing Malwares
Two weeks ago I had a hunch that some Malwares were being distributed through phishing URLs/links. The process involves analyzing phishing feeds from known sources (openphish/phishtank) and loading them up on headless chrome to see if I can find APK/IPA link or official store links that might be affiliated to the attackers.
This method has two advantages
- Build malware dataset
- Catch botnets early
Architecture
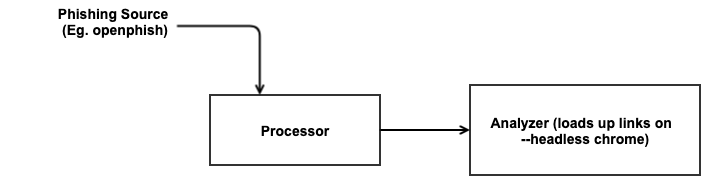
The processor block download feeds from (openphish/phishtank) and dispatches phishing links to the analyzer block which loads up the request on headless chrome.
Deplyment
Using GCP,
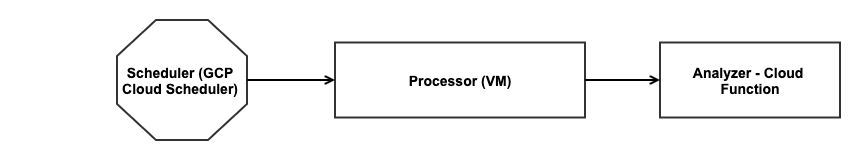
I have cloud scheduler that launches the processor vm twice a day to download the feed and start dispatching links to the analyzer. The scheduler then kills this instance after three hours. This decision was done to reduce the complexity of the system. Future updates will kill this instance once the task at hand is completed.
The analyzer is deployed on Google Cloud Functions. It’s a node application that has headless chrome installed on its runtime environment.
Danger Zone
Follow at your own risk,
You can follow the results on the below telegram channel. It will report caught malware links